Victims of cyber attacks are not only limited to international companies or multinationals. Unfortunately, any company that has a computer system that hosts personal or confidential data can fall prey to hackers.
One of our own, in Quebec, has recently fell victim to such a crime. The Cégep de Saint-Félicien has confirmed that there was a data theft following a cyber attack on September 17th. We refer you to the following article (available in French only).
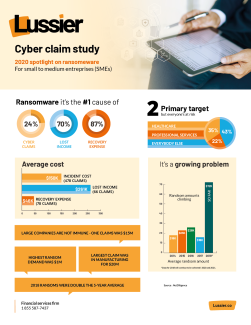
A cyber attack can produce disastrous consequences. The associated costs can be very significant to restore your systems, not to mention the impact of a business interruption if the hacker paralyzes and takes your computer systems hostage. Many hackers will also demand a ransom of up to $100,000 to unlock your systems. As an entrepreneur, you need to ask yourself if you are financially strong enough to survive such an attack and if you have the resources available to respond quickly. In the case of the Cégep de Saint-Félicien, this attack “could cost hundreds of thousands of dollars, even close to a million dollars. »
Provincial and federal laws impose very specific responsibilities on you with respect to your obligation to protect the personal and confidential information of your customers, suppliers and employees. In Canada, the Office of the Privacy Commissioner oversees compliance with the Personal Information Protection and Electronic Documents Act (PIPEDA). In Quebec, the Act respecting the protection of personal information in the private sector applies to the activities of provincial companies within the province. These laws have the power to impose significant fines and penalties. Be wary to believe that transferring this data to an external supplier exempts you from this obligation; it is not possible to transfer your legal obligations to a third party. Ultimately, you remain responsible for the data entrusted to you.
If you have international clients, each country has its version of similar laws that impose responsibilities to customers, even if you are a Canadian company. For example, the European Union has implemented the General Data Protection Regulation (GDPR). This Regulation can impose penalties of up to 20 million euros or 4% of your worldwide turnover.
According to statistics, one of the most frequent and expensive exposures is ransom software and taking your systems hostage. Ransom demands average $72,000, but can escalate very quickly to hundreds of thousands of dollars. The loss due to business interruption can also be very significant. Imagine not having access to your systems for a few days, or even weeks! Lest you forget the reputational impacts as well.
Fortunately, there are insurance products that can help mitigate the financial effects of such attacks. In fact, you can transfer the risks associated within the cyber world to an insurance policy and the various experts who would handle an attack. The “Cyber Risk” policy provides coverage that protects the insured, not only for the direct costs associated with an attack, but also for your liability to third parties. Here are some examples of the coverages available.
Direct costs:
- Services and fees related to an invasion of privacy (e.g., forensic and computer expertise fees, notification fees, credit monitoring)
- Crisis management fees
- Threats of extortion (e.g., ransom money)
- Operating losses/Additional expenses
- Data protection and system recovery
- Reward fee
- Social Engineering Fraud
- Computer Fraud
- Fraudulent funds transfers
Expenses related to your civil liability:
- Network Security and Privacy Liability: The loss or unauthorized disclosure of personal information, the inability of authorized third parties to access the insured’s operating system, the transmission of malicious code, damage to or loss of third party data in the care, custody and control of the insured, failure to promptly disclose a network security breach, or vicarious liability when the insured entrusts data to a third party (e.g., hosting).
- Media and Advertising Liability: Personal injury, infringement of copyright or other form of intellectual property or any other wrongdoing, relating to objects published on the insured’s website.
For more information, please contact your broker. At Lussier, we have expertise in cyber risks and privacy infringement as well as risk management.




